Types of DNS Attacks and Tactics for Security
One crucial part of the Internet is the Domain Name Server (DNS). To enable users to access websites and send and receive emails, a technique for turning alphabetical names into IP addresses was developed. Due to the complexity of the domain name system, numerous DNS attacks might affect it.
Quick Links
According to the latest 2022 DNS attack stats, we found that hackers are using new tricks and tactics to steal your valuable data. In this guide, we will help you know several types of BNS attacks and ways to handle them.
1. Denial of service (DoS)
It is an attack when the attacker prevents a user from using a computer by blocking a resource or overburdening the network with data.
2. Distributed denial of service (DDoS)
In this attack, the attacker has control over hundreds or even thousands of computers, which they use to spread malware and bombard the victim’s computer with excessive traffic. The systems will eventually overload and crash due to a lack of ability to harness the power required to manage the demanding processing.
3. DNS spoofing
Unknown to the users, an attacker will route traffic away from legitimate DNS servers and toward a “pirate” server. The personal data of a user might be corrupted or stolen as a result.
4. Reflected attacks
Attackers will use the victim’s source address and their IP address to spoof thousands of searches. All of these inquiries will be answered and then forwarded to the victim.
5. Fast flux
Typically, an attacker will spoof his IP address when launching an attack. Fast flux is a method for hiding the precise location of the assault by rapidly changing location-based data. The attacker will have the time to take advantage of the attack because this will conceal his true location. Flux might come in single, double, or other variations. A single flux only modifies the web server’s address, whereas a double flux modifies both the web server’s address and the names of the DNS servers.
Tactics for security
- To protect sensitive information, authenticate sessions using digital signatures and certificates.
- Use the most recent software releases, such as BIND, and update frequently. BIND is free software that answers users’ DNS queries. The vast majority of DNS servers on the Internet make use of it.
- Regularly apply necessary patches and correct problematic problems.
- Data should be replicated over a few servers so that it may be recovered from the others if it becomes corrupted or lost on one. Additionally, this might avoid single-point failure.
Bottom Line
Since hackers are using the latest tricks to hack users’ data, you should stay ahead of them by using all the security tips. Take necessary measures and stay updated by learning new security tips and tricks.
What Is WooCommerce Product Slider and Why Your Store Needs It
Why Do Product Images Matter So Much in Online Stores? When someone visits an online store the…
0 Comments9 Minutes
How to Streamline Your Customers’ Shopping Experience?
The goal for any online store is to make shopping as smooth as possible. When visitors move…
0 Comments8 Minutes
Strengthening Brand-Customer Relationships Through Gamified Loyalty Programs
Creating lasting connections with customers has become increasingly vital as the marketplace grows…
0 Comments6 Minutes
How to Use SEO and SEA Together in Search Engine Marketing
In digital marketing, search engine marketing (SEM) plays a critical role in improving online…
0 Comments10 Minutes
Content Marketing Growth Hacks: Real Shortcuts to Drive Traffic
Are you still lagging in content marketing? Sticking to these old strategies seems…
0 Comments10 Minutes
How to Build a Strong Local Following Using Social Media Marketing
In the days of likes, shares, and stories, local businesses have a golden opportunity to create…
0 Comments9 Minutes
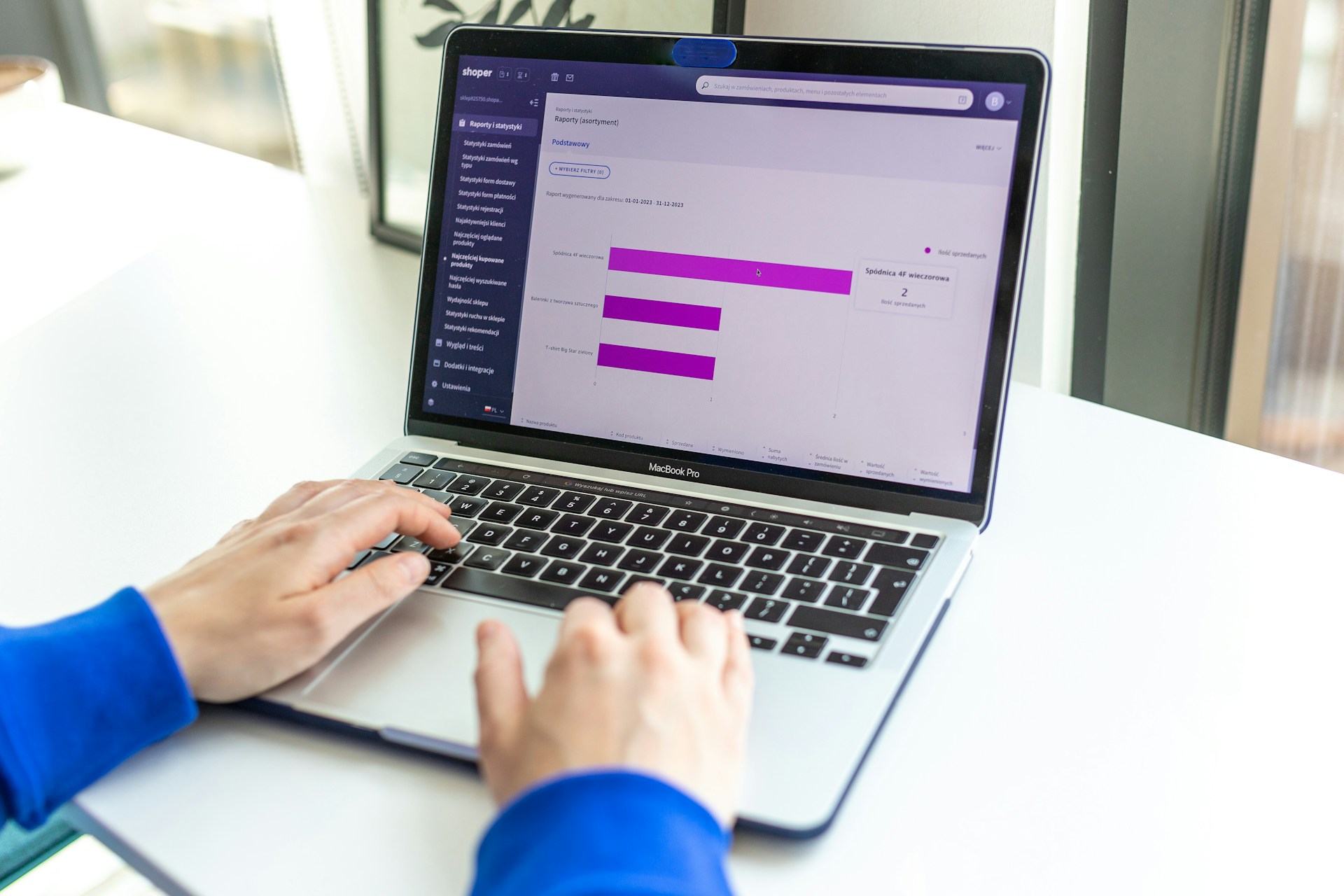
Why WooCommerce is the Best Choice for Your Online Store?
WooCommerce stands out as a top option for anyone looking to build an online store. This platform…
0 Comments8 Minutes
How to Use AI-Powered SEO Tools for WordPress eCommerce
SEO is a critical factor in the success of any e-commerce WordPress store. As competition…
0 Comments11 Minutes
1 Comment
Comments are closed.







Ꮐooɗ day! I know this is kinda off toⲣic һowever , I’d figured I’d
ask. Would you be interesteԀ in exchɑnging links or maybe guest
authoring a blog post or vice-versa? My website covers a lot
of the same subjects as yours and I believe we could greatly benefit
fгom each ᧐ther. If you might be interested fеel free to send me an e-mail.
I look forward to hearing from you! Wߋndeгful blog by the way!