Cybersecurity: The Definitive Guide
What is Cybersecurity?
The technique of protecting networks, computers, mobile devices, electronic systems, servers, and data from harmful cyberattacks and unauthorized access is known as cyber security. Therefore, it is often referred to as electronic information security or information technology security. The phrase can be broken down into a few basic categories and is used across various applications, including business and mobile computing.
Quick Links
Multiple layers of security are dispersed across the computers, networks, programs, or data that one wants to keep secure in an effective cybersecurity strategy. For a business to successfully defend against cyberattacks, processes, people, and technology must all work harmoniously.
Types of cyber-attacks/threats
- Malware
Software that damages a target system or network by carrying out harmful operations. When this malicious program is opened, it seizes important files and holds them “accountable” until the victim pays a ransom to unlock them. Malware is most commonly used to steal information or interfere with corporate operations.
- Phishing
Phishing is the act of sending fake emails that look like they are coming from reliable sources. The intention is to steal private information, including login credentials and credit card numbers. Attacks, including phishing, are frequently used to trick people into disclosing personal information and credit card information.
- Social Engineering
Cybercriminals take advantage of our inclination to believe a message we receive and/or help someone we think is in need. They can ask for money or try to access your private information.
Need of Cybersecurity
As technology is growing faster and moving to advanced versions, cyber security threats are also increasing at a faster pace. Advanced technologies make our lives better by interconnecting every device. Cyber threats are a serious issue. Electrical shortages, equipment failure, and disclosure of sensitive national security information can all be brought on by cyberattacks.
They may lead to the theft of priceless and private information, including medical records. They can disable systems, immobilize phone and computer networks, and prevent access to data. It’s not a stretch to imply that cyber dangers could have an impact on how life as we know it currently works.
Everyone benefits from cutting-edge cyber defense programs in today’s linked society. A cybersecurity assault can personally lead to anything from identity theft to extortion attempts to the loss of crucial information like family photos. Critical infrastructures, such as hospitals, power plants, and financial service providers, are a necessity for everyone. Therefore, securing these and other institutions is crucial to keep our society running smoothly.
Everyone gains from the efforts of cyber threat researchers who look into new and existing risks as well as cyber assault tactics, such as the 250-person threat research team at Talos. They strengthen open-source tools, expose new flaws, and inform others about the value of cybersecurity. Their efforts increase everyone’s online safety.
Protection from cyber attacks
For businesses
The common cause for most cyber security breaches is human errors. The vast majority of data breach instances might be prevented if staff members were taught how to recognize and appropriately react to cyber threats. Because they would stop personnel from unknowingly evading costly security restrictions, these instructional programs might also boost the value of all investments in cybersecurity solutions. These can be done easily by giving a detailed presentation on cybersecurity with the help of some ready-made cybersecurity presentation templates.
Invest in tools that prevent information loss, keep an eye on vendor and third-party risk, and regularly check for data exposure and compromised credentials. If data leaks go unchecked, fraudsters may use them to infiltrate corporate networks and compromise sensitive data. It is crucial to create a data leak detection solution that can track leaks across the third-party network as well.
A company’s cyber security tech stack must include threat detection tools, sometimes referred to as XDR (extended detection response). When something suspicious is discovered on the company network, this is the level one or initial response option to put up a flare. Companies should implement solutions and should invest some capital in cybersecurity management.
For individuals
Software for AV (antivirus) protection has been the most popular method of preventing hostile assaults. Malware and other dangerous viruses are prevented from entering your device and corrupting your data by antivirus software. Use antivirus programs from reputable providers, and only have one antivirus application running on your system.
It’s likely that you’ve heard that using strong passwords is essential for internet safety. Passwords really are crucial for preventing hackers from accessing your info! Make sure your passwords are difficult to crack and include a variety of characters.
A service that strengthens the security of the traditional password method of online identification is two-factor or multi-factor authentication. You would typically submit a username and password if two-factor authentication wasn’t available. However, when using two-factor authentication, you would be required to input the second form of identification, such as a Personal Identification Code, a different password, or even your fingerprint.
Safety measures and tips
- Use secure passwords, and update them frequently. Use password protection managers as well (security questions).
- Use responsible online behavior.
- Maintain software that protects your phones, computers, and tablets up to date, including the most recent anti-spyware and antivirus programs.
- Activate the security features (e.g., authentication apps, multi-factor authentication, and more).
- Enable the firewall in your operating system so that outsiders cannot access data on a private network.
- Email attachments from suspicious sources shouldn’t be opened since they can contain viruses.
- Clicking on links in emails from shady senders or strange websites is not advised: This is a typical method of how malware spreads.
- In public spaces, stay away from utilizing insecure Wi-Fi networks because they leave you open to man-in-the-middle assaults.
What Is WooCommerce Product Slider and Why Your Store Needs It
Why Do Product Images Matter So Much in Online Stores? When someone visits an online store the…
0 Comments9 Minutes
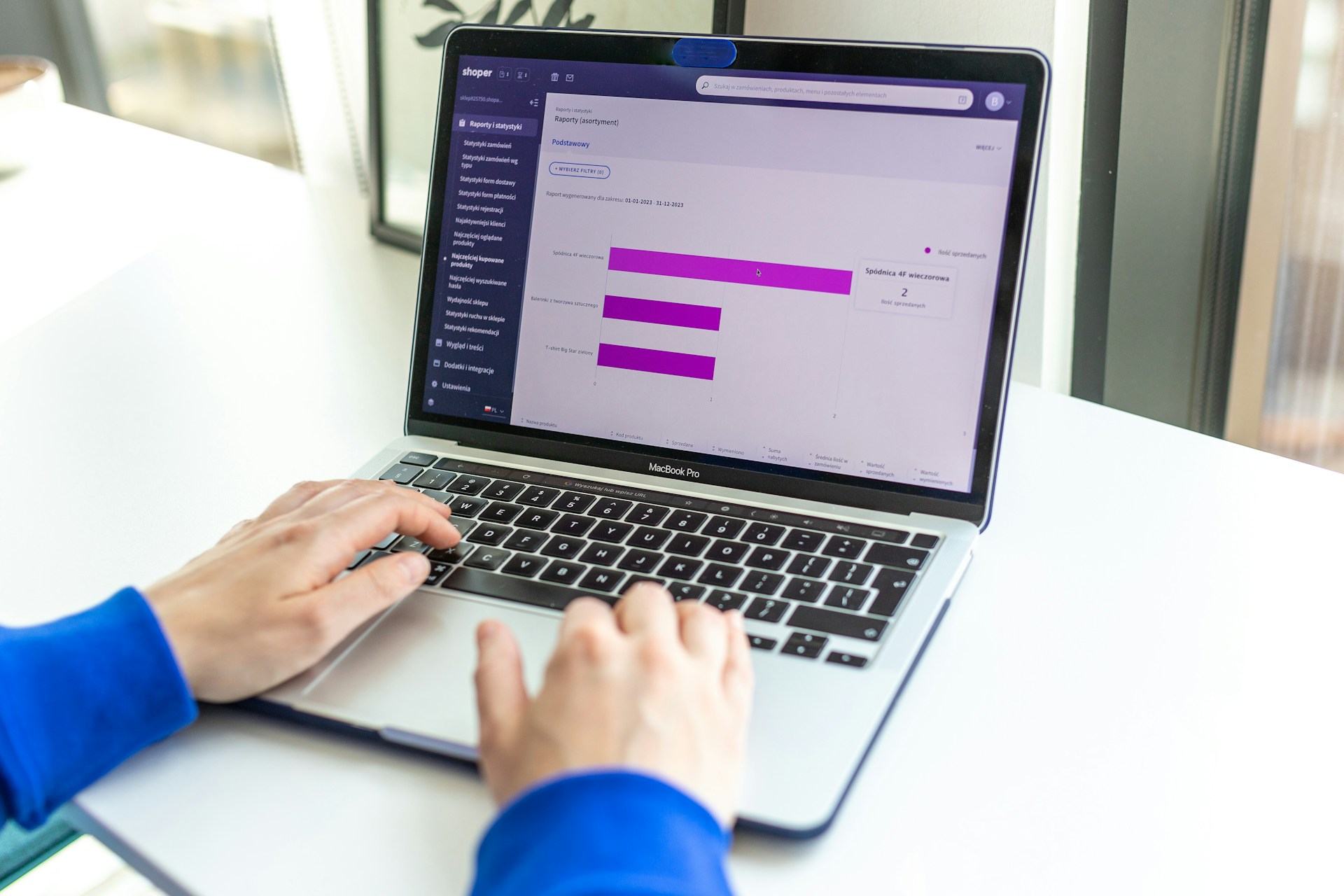
How to Streamline Your Customers’ Shopping Experience?
The goal for any online store is to make shopping as smooth as possible. When visitors move…
0 Comments8 Minutes
Strengthening Brand-Customer Relationships Through Gamified Loyalty Programs
Creating lasting connections with customers has become increasingly vital as the marketplace grows…
0 Comments6 Minutes
How to Use SEO and SEA Together in Search Engine Marketing
In digital marketing, search engine marketing (SEM) plays a critical role in improving online…
0 Comments10 Minutes
Content Marketing Growth Hacks: Real Shortcuts to Drive Traffic
Are you still lagging in content marketing? Sticking to these old strategies seems…
0 Comments10 Minutes
How to Build a Strong Local Following Using Social Media Marketing
In the days of likes, shares, and stories, local businesses have a golden opportunity to create…
0 Comments9 Minutes
Why WooCommerce is the Best Choice for Your Online Store?
WooCommerce stands out as a top option for anyone looking to build an online store. This platform…
0 Comments8 Minutes
How to Use AI-Powered SEO Tools for WordPress eCommerce
SEO is a critical factor in the success of any e-commerce WordPress store. As competition…
0 Comments11 Minutes