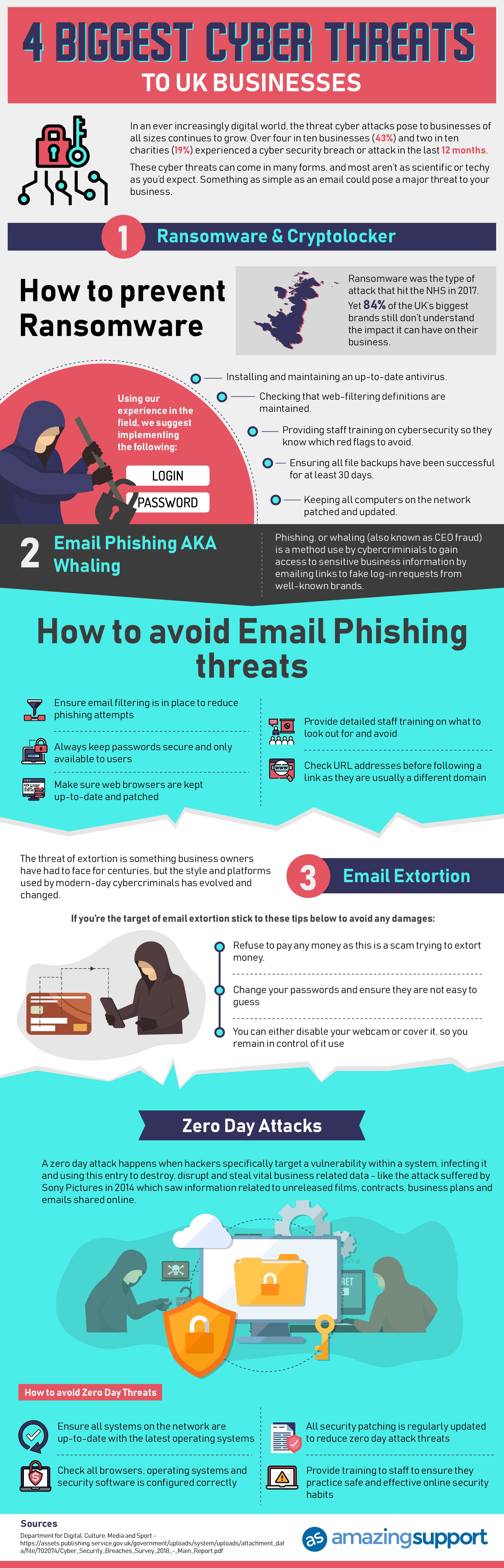
Cyber Attacks Are a Real Threat – Even For Small Businesses
Cyber crime is no more a new phenomenon. The motivation with which criminals carry out this act has been a major concern for small businesses and organizations. Cybercriminals are constantly looking for new sites and servers to attack. They are regularly refining their means of attack. Worst is that these attacks are very difficult to detect and solve.
There is no threat that has advanced so fast, in a way that is hard to understand, like cyber attacks. A cyber attack is an offensive maneuver carried out by individuals or organizations on infrastructures, computer information systems and computer networks by various malicious acts, originating from an unknown source with the aim of stealing, altering or destroying its targets information.
In the UK, 99.6% of businesses are Small and Medium Businesses (SMBs), and even though 38% of them think they are too small to become targets, 35% of them have been attacked in the last 12 months. 26% of SMBs who were attacked were used as entry points to bigger organizations they supply to, leading to damaged relationships with their customers and even worse, information being stolen. With about 4000 daily ransomware attacks since the beginning of 2016, it is important to take cyber security protection seriously.
Targetting small businesses:
Cyber criminals and hackers in London and around the world consider small businesses as easy picking. These companies are connected to larger targets, but have little or no protection, leaving so many security loopholes that are related to most activities carried out there, such as making use of public hotspots or using someone else’s USB stick.
There are many entry points for hackers and cyber criminals, these include:
- Emails: which is the most common entry point for them, mostly through malicious attachments, with 91% of cyber attacks originate from a phishing email
- IT services: an IT network that has no good protection, together with servers or workstations having no security updates can be an easy entry point, especially for worms which are able to automatically propagate
- Advertising banners: some banners, particularly on free sites can be hacked when clicked and trigger a malware download
- Applications: particularly those on Android devices have lesser checks than those on iOS devices
- Networks: using insecure networks such as public hotspots are ideal ways of intercepting communications and recover passwords and data
- Connected devices: these devices can be accessed remotely, making them vulnerable and allowing hackers to piggyback into the network of a company
- Ecosystem: a company and its suppliers having a trusted relationship could lead to carelessness. When one part of that chain is left unprotected, it can be used as a weak link by cyber criminals to launch an attack
- USB stick: That unrecognisable USB sticks could contain malicious software, intentionally left there. Avoid opening it while using a computer connected to the network of the company.
- Humans: some dubious ‘insiders’ such as IT consultants could carry out this attack, however, this is only in very rare cases.
Although many companies have put measures in place to prevent cyber attacks, statistics reveal that only big organisations are doing what they need to do. Smaller businesses either assume they cannot afford good protection or they don’t need it. Protection from cyber attacks is expensive – it involves a lot of work, including risk assessment, training of employees and installation of some programs that can effectively detect intrusion. But it is all very worth the work.
There are other methods small businesses can have quality protection, and it is important they do so. Any data breach could cost your company a lot of money. Most experts look at it as a not a matter of IF you get attacked, but WHEN. Prevention is the best method in dealing with cyber attacks. Even though this seems expensive, it can save your company a lot more.
If you wish to use this infogrphic in your website then please use the following code:
Author
David Share, Director at Amazing Support IT London

David has held positions as Operations Director and Head of IT in legal and professional firms for more than 10 years. He is a Director and co-owner of Amazing Support, a Microsoft Silver & Cyber Essentials accredited specialist Managed IT Support and Cyber Security company. David actively helps SME businesses receive better Managed IT Support and Cyber Security Services in the London and Hertfordshire areas. He also assists overseas companies who are looking to expand their business operations into the UK and helps with their inward investment IT process. A member of The Chartered Institute for IT (BCS), UK Council for Child Internet Safety (UKCCIS) and an event speaker promoting business start-ups and technology awareness.
How to Improve Customer Experience With a Loyalty Program
Customer experience and satisfaction are the needs of every business today! With the global…
0 Comments9 Minutes
The Role of AI-driven Marketing Automation in Streamlining Workflows
Information overload has left brands grappling with the challenge of tackling vast amounts of data…
0 Comments12 Minutes
Critical Challenges in Automation Testing and How to Overcome Them
Software development methods now include automation testing as a necessary component because of…
0 Comments8 Minutes
How to Scale Your Business with Pimcore Development Services
In the quickly evolving digital world, companies are always looking for creative ways to move…
0 Comments8 Minutes
What are Niche Edits?
A link-building tactic known as "niche edit" is when publishers or website owners enhance…
0 Comments12 Minutes
Understanding the importance of Metadata and busting the common myths
Metadata is an important aspect of the website. It gives to the search engines about what a…
0 Comments8 Minutes
Common Data Migration Challenges and How to Overcome Them
In the era of technology, data serves as the backbone of companies. Whether it's client details,…
0 Comments13 Minutes
SIEM at a glance (Security information and event management)
You have a contingency plan like most other intelligent businesses, but what if it fails? And,…
0 Comments12 Minutes