Alternatives to IP Whitelisting: Is It Really Essential?
When it comes to setting up an internet network for your company, security is crucial. One of the many practices companies employ in their cyber security plan is IP whitelisting. Every practice has its positive and negative sides according to your business needs. Knowing what IP whitelisting is might help you decide if it’s the best option for your company.
Quick Links
What is IP whitelisting?
In the context of cyber security, a whitelist is a list of IP addresses, email addresses, and apps that have been accepted by the administrator. Whitelisted items are given access to the system, enabling them to be installed, changed, and communicated with via the private network. A whitelist’s purpose is to protect a private network and its devices against external threats.
Therefore, IP whitelisting is a method of granting trusted people access to your company’s network. The network administrator can use an IP whitelist to enable particular IP addresses to remotely access your files, apps, and software. If your organization employs cloud services, for example, you could want to restrict access to the cloud to people with IP addresses from your office.
Pros of IP whitelisting
Improved security
You can improve system security by employing IP whitelisting, which prevents unwanted access to your network. If an IP address that isn’t whitelisted tries to connect to your network, they will be refused access.
For instance, let’s think that a hacker attempted to log in using stolen credentials. However, if the IP address connected to those credentials has been whitelisted, the hacker will have difficulty gaining access to the system network. Even if the credentials have been exposed, the hacker must connect from a whitelisted IP address.
More productivity
At work, most employees nowadays choose to use their cellphones and other personal devices. BYOD (Bring Your Own Device) policy raises the danger of cyberattacks. Multiple devices on an insecure network expose firms to insider assaults that are either irresponsible or unintentional. There are also extra distractions that come with multiple devices. According to a study, employees view nearly an hour of non-work-related media every day on average.
Whitelisting enables businesses to create their own BYOD rules on their own terms. Whitelisting allows organizations to block insecure and distracting websites that might jeopardize company initiatives and reduce productivity.
In addition, system crashes and delays are dramatically minimized when only whitelisted IPs are permitted access, even when resources expand. This provides you with more productivity since you’ll have one less problem to deal with.
Compatibility with third-party applications
Diversified cyber security plans are always more advanced and effective. Anti-ransomware, anti-malware, and anti-virus software, as well as penetration testing to look for vulnerabilities in your network, are all important cyber security practices. Whitelisting is a good fit for this strategy. It works well with other software and adds another tool to your cyber armory.
Cons of IP whitelisting
Reduces web traffic
Whitelisting IP addresses can reduce web traffic to your website since it restricts access. This might hinder potential customers or clients from visiting your page if you have a commercial website.
Can be time-consuming
Every user and IP address must have their access privileges assessed and applied, and businesses must update their whitelist every time new software or patch is installed. Especially if you have a large system, this may become a hassle for you.
However, you can get around this by employing a more advanced IP whitelisting service that doesn’t leave much work to you. You can check out this page to learn more about an advanced IP whitelisting option.
Is whitelisting right for your company?
As mentioned above, whitelisting can have some disadvantages. But there are solutions for you to eliminate these disadvantages so that you can benefit from IP whitelisting as a part of your cyber security toolbox.
For example, you can implement a SaaS access control over the VPN between your resources and external traffic. Instead of whitelisting each device’s IP address, IT administrators can simply whitelist the VPN gateway’s dedicated static IP address.
This is a highly easy technique to simplify the complexity of IP whitelisting while maintaining a high degree of security with contemporary cloud VPNs, which also allow zero-trust access control.
IP whitelisting is part of the solution
Whitelisting IP addresses is an excellent strategy to keep unwanted visitors off your network. When an IP address is added to the whitelist, it allows you and other users with that IP address to view those pages, while everyone else is prohibited. This keeps data safe and secure and helps you protect against cyber attacks.
Although whitelisting IP addresses is not the final solution to security issues, it can dramatically improve the safety of organizational resources when done correctly. If you decide to expand your cyber security toolbox by implementing IP whitelisting, you should choose a provider that has a good reputation.
What Is WooCommerce Product Slider and Why Your Store Needs It
Why Do Product Images Matter So Much in Online Stores? When someone visits an online store the…
0 Comments9 Minutes
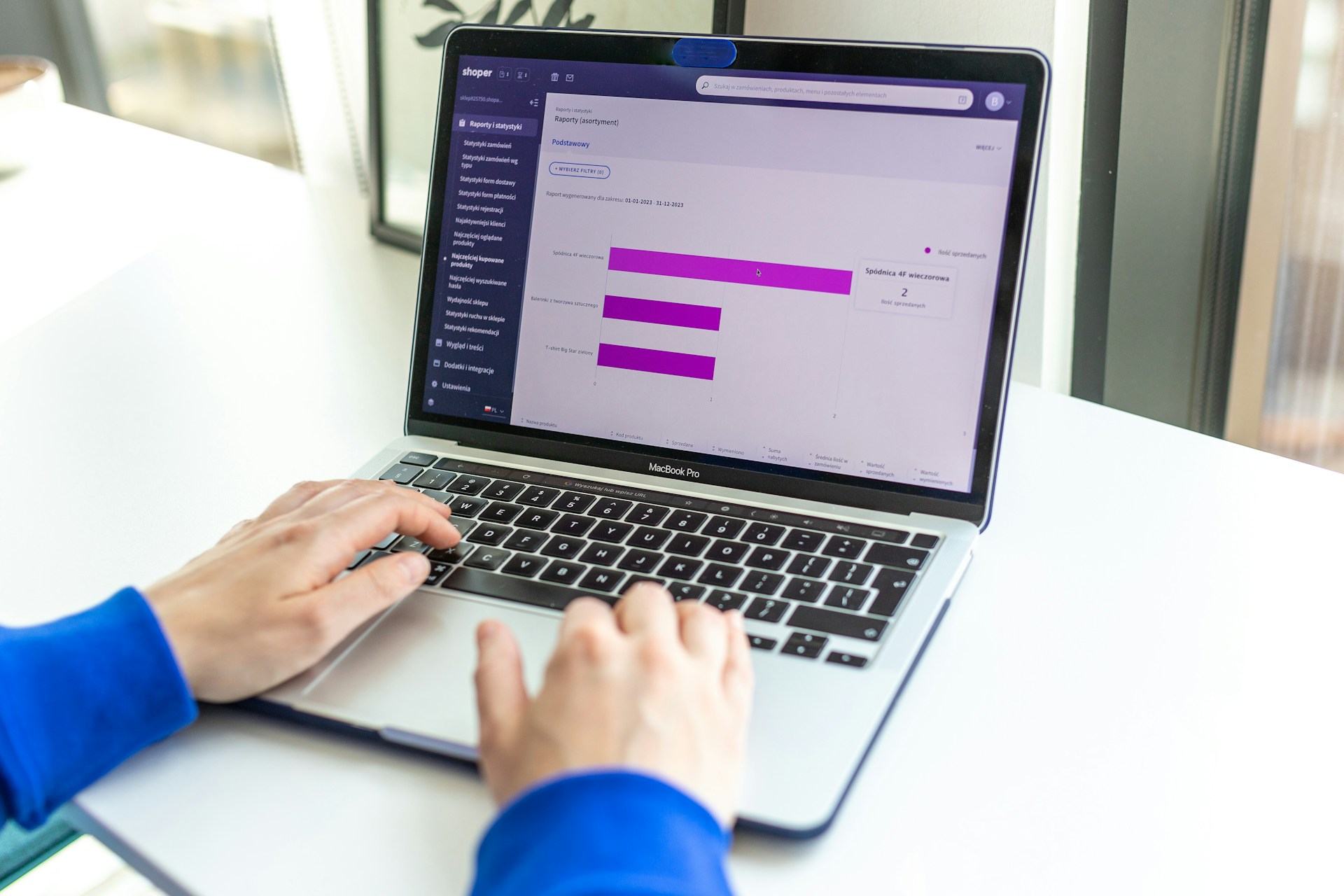
How to Streamline Your Customers’ Shopping Experience?
The goal for any online store is to make shopping as smooth as possible. When visitors move…
0 Comments8 Minutes
Strengthening Brand-Customer Relationships Through Gamified Loyalty Programs
Creating lasting connections with customers has become increasingly vital as the marketplace grows…
0 Comments6 Minutes
How to Use SEO and SEA Together in Search Engine Marketing
In digital marketing, search engine marketing (SEM) plays a critical role in improving online…
0 Comments10 Minutes
Content Marketing Growth Hacks: Real Shortcuts to Drive Traffic
Are you still lagging in content marketing? Sticking to these old strategies seems…
0 Comments10 Minutes
How to Build a Strong Local Following Using Social Media Marketing
In the days of likes, shares, and stories, local businesses have a golden opportunity to create…
0 Comments9 Minutes
Why WooCommerce is the Best Choice for Your Online Store?
WooCommerce stands out as a top option for anyone looking to build an online store. This platform…
0 Comments8 Minutes
How to Use AI-Powered SEO Tools for WordPress eCommerce
SEO is a critical factor in the success of any e-commerce WordPress store. As competition…
0 Comments11 Minutes